A one-time password (OTP) is a password that is valid for only one login session or transaction, on a computer system or other digital device. OTPs avoid a number of shortcomings that are associated with traditional (static) password based authentication; a number of implementations also incorporate two factor authentication by ensuring that the one-time password requires access to something a person has (such as a small keyring fob device with the OTP calculator built into it, or a smartcard or specific cellphone) as well as something a person knows.
The most important advantage that is addressed by OTPs is that, in contrast to static passwords, they are not vulnerable to replay attacks. This means that a potential intruder who manages to record an OTP that was already used to log into a service or to conduct a transaction will not be able to abuse it, since it will be no longer valid. A second major advantage is that a user who uses the same (or similar) password for multiple systems, is not made vulnerable on all of them, if the password for one of these is gained by an attacker. A number of OTP systems also aim to ensure that a session cannot easily be intercepted or impersonated without knowledge of unpredictable data created during the previous session, thus reducing the attack surface further.
OTPs have been discussed as a possible replacement for, as well as enhancer to, traditional passwords. On the downside, OTPs are difficult for human beings to memorize. Therefore they require additional technology to work.
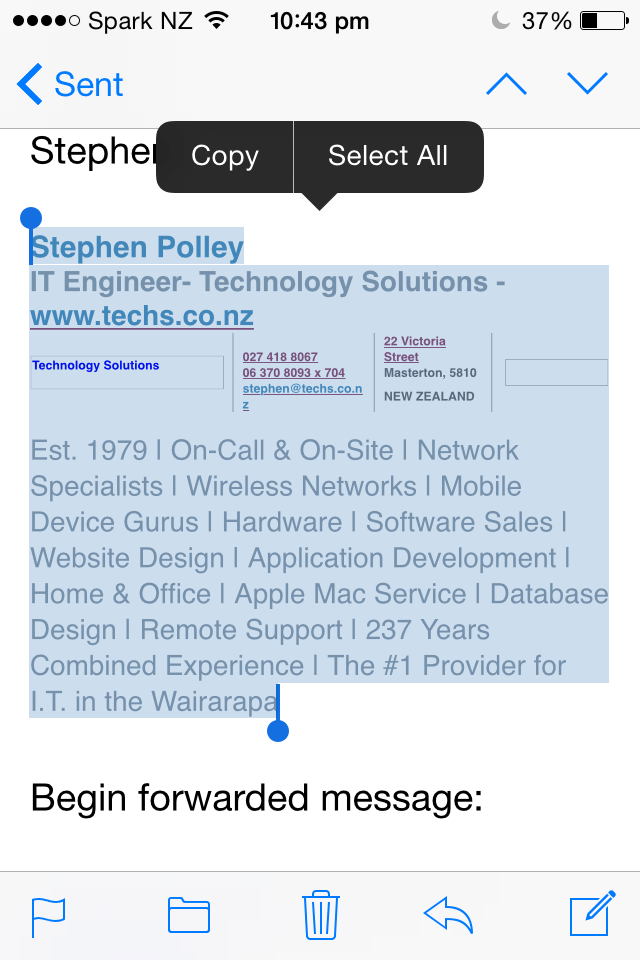
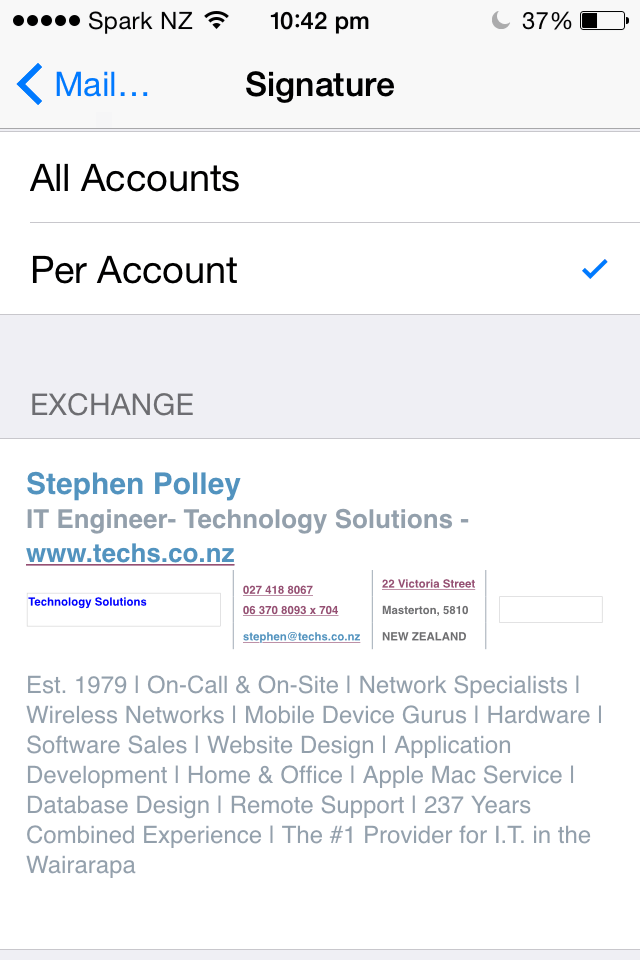
An extra layer of security that is known as “multi factor authentication”
In today’s world of increasing digital crime and internet fraud many people will be highly familiar with the importance of online security, logins, usernames and passwords but if you ask them the question “What is Two Factor Authentication?” the likelihood is they will not know what it is or how it works, even though they may use it every single day.
With standard security procedures (especially online) only requiring a simple username and password it has become increasingly easy for criminals (either in organised gangs or working alone) to gain access to a user’s private data such as personal and financial details and then use that information to commit fraudulent acts, generally of a financial nature.
How does it work?
Two Factor Authentication, also known as 2FA, two step verification or TFA (as an acronym), is an extra layer of security that is known as “multi factor authentication” that requires not only a password and username but also something that only, and only, that user has on them, i.e. a piece of information only they should know or have immediately to hand – such as a physical token.
Using a username and password together with a piece of information that only the user knows makes it harder for potential intruders to gain access and steal that person’s personal data or identity.
Historically, two-factor authentication is not a new concept but its use has become far more prevalent with the digital age we now live in. As recently as February 2011 Google announced two factor authentication, online for their users, followed by MSN and Yahoo.
Many people probably do not know this type of security process is called Two-Factor Authentication and likely do not even think about it when using hardware tokens, issued by their bank to use with their card and a Personal Identification Number when looking to complete Internet Banking transactions. Simply they are utilising the benefits of this type of multi factor Authentication – i.e. “what they have” AND “what they know”.
Using a Two Factor Authentication process can help to lower the number of cases of identity theft on the Internet, as well as phishing via email, because the criminal would need more than just the users name and password details.
So if you’re in need of some help securing your system, or even just some free friendly advice, get in touch with us on 0800 878 878 or email office@techs.co.nz